PeopleSoft 9.2: Understanding Fluid Security-Peoplesoft Modernization

Table of Contents
PeopleSoft Application on the fluid platform is gaining a lot of attention. Organizations have started thinking about giving their end users a cohesive and unified experience across platforms by enabling the fluid option. However as they start preparing for this transition, there are several factors to consider.
Security is one such parameter that needs due attention. With Fluid, end users can be more empowered to build their own ‘customized version’ of their PeopleSoft world. They can create their homepages, or alter the content they want to see on the delivered homepages. The IT team can configure and build a lot of content that can be pushed out to the end users. This also implies, that the controls and checks need to be in place to ensure that both the users and the IT team have the right security to perform certain transactions and also to ‘Not’ perform certain transactions!
Want to learn more about PeopleSoft on the Fluid platform?
Access resources provided by Astute professionals to make a well-informed decision before transitioning to PeopleSoft on Fluid.
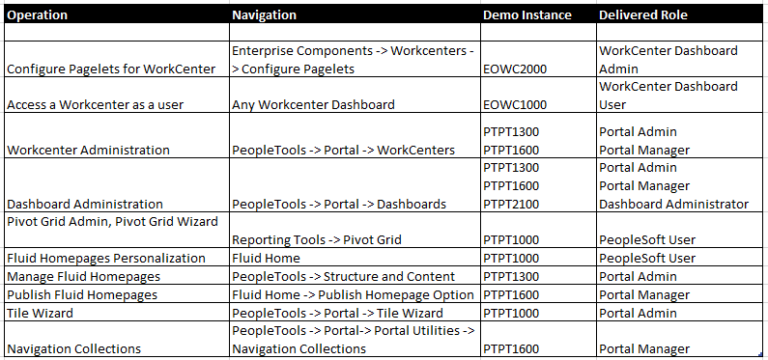
This is a matrix I created to understand how to design security by identifying the exact roles and permission lists needed to perform critical actions:
It is important to keep these considerations in mind before transitioning in order to make a well-informed decision. Especially in today’s time when data security has become so crucial for businesses, it is imperative that you take the right steps in this direction.
At Astute, we aim to empower businesses by providing them with ample resources to understand their working ecosystems in a more comprehensive way. Should you require any further assistance, feel free to contact us right away!
Let us assist you
Empower your team with a robust working infrastructure.
Jiyash is the Head of Cloud and AI engineering at Astute. He has over 24 years of experience in IT consulting and project management experience in ERP and Oracle cloud migration projects, Jiyashhas executed complex PeopleSoft ERP upgrades and global rollouts in Peoplesoft Human Capital Management and Finance/Supply Chain across the globe.
Search
Tags
Related Posts
Subscribe Our Newsletter
Gain access to exclusive insights, technical know-how and crucial knowledge from Astute experts.
Share Article
See The Team In Action
Upcoming Events

- Accounts Payable - AP
- AI Agents
- AI for ERP
- GenAI
AI for ERP in Action: Built for Enterprise Operations

- Accounts Payable - AP
- Higher Education
- AI Agents
- AI for ERP
- GenAI
Modernizing Accounts Payable: Built for Real Operations
Reach Out
Ready to Connect?
Please fill the following form, we will get back to you within a business day.
Contact Form
Contact Us
-1.png)
.png)
-1.png)
